How phishing attacks evade traditional security defenses
Tech Republic Security
MARCH 30, 2021
Two of three phishing pages analyzed by Armorblox were hosted on legitimate services to try to sneak past the usual security protection.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Tech Republic Security
MARCH 30, 2021
Two of three phishing pages analyzed by Armorblox were hosted on legitimate services to try to sneak past the usual security protection.

eSecurity Planet
AUGUST 23, 2023
Spear phishing is a more targeted and effective phishing technique that attempts to exploit specific individuals or groups within an organization. While phishing uses a broader range of tactics, such as mass emailing to random recipients, spear phishing is often well-researched and tailored to high-value targets.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
SC Magazine
MAY 11, 2021
Researchers last week spotted a phishing campaign that leveraged an online email authentication solution from Zix, in hopes that potential victims would be lulled into a false sense of security. The post Zix tricks: Phishing campaign creates false illusion that emails are safe appeared first on SC Media.

Tech Republic Security
MARCH 11, 2020
A Trend Micro report finds that spammers are using public and hosted cloud infrastructure to slip malicious emails past security defenses.

Security Affairs
APRIL 25, 2019
Experts at Proofpoint discovered that free code repositories on GitHub have been abused since at least 2017 to host phishing websites. Researchers at Proofpoint reported that crooks are abusing free code repositories on GitHub to host phishing websites and bypass security defenses. Pierluigi Paganini.

Security Affairs
FEBRUARY 28, 2024
Emerging Threats and Trends The landscape of email threats continues to evolve, with VIPRE’s report shedding light on several alarming trends: Deepfake and AI Exploitation: Attackers increasingly leverage deepfake technology and AI to craft more convincing phishing emails, significantly raising the stakes for email security.

Threatpost
MARCH 11, 2020
Attackers are using YouTube redirect links, whitelisted by various security defense mechanisms, to evade detection.

Threatpost
FEBRUARY 4, 2021
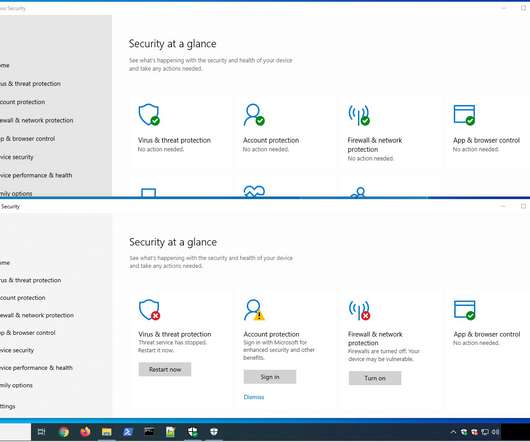
A savvy phishing campaign manages to evade native Microsoft security defenses, looking to steal O365 credentials.

SC Magazine
JULY 6, 2021
Microsoft CEO Satya Nadella has been a strong proponent for average users facing phishing scams, especially during the COVID-19 pandemic. Today’s columnist, Tony Pepper of Egress, writes about how people have become the new perimeter and they must be properly trained to spot phishing attacks. They’re also not perfect.
eSecurity Planet
JULY 13, 2023
“WormGPT produced an email that was not only remarkably persuasive but also strategically cunning, showcasing its potential for sophisticated phishing and BEC attacks” (screenshot below). ” Just last week, Acronis reported that AI tools like ChatGPT have been behind a 464% increase in phishing attacks this year.

Webroot
APRIL 4, 2022
High-risk URLs are phishing for your data in the most benign of locations. To make matters worse, almost 66% of them involved phishing. Our complete list of top brands that are most impersonated is available in the phishing section of our full report. Thwarting cyber threats through cyber resilience.

CyberSecurity Insiders
FEBRUARY 2, 2022
.–( BUSINESS WIRE )– Menlo Security , a leader in cloud security, today announced it has identified a surge in cyberthreats, termed Highly Evasive Adaptive Threats (HEAT), that bypass traditional security defenses. The top three brands impersonated in phishing attacks are Microsoft, PayPal, and Amazon.
Cisco Security
AUGUST 17, 2021
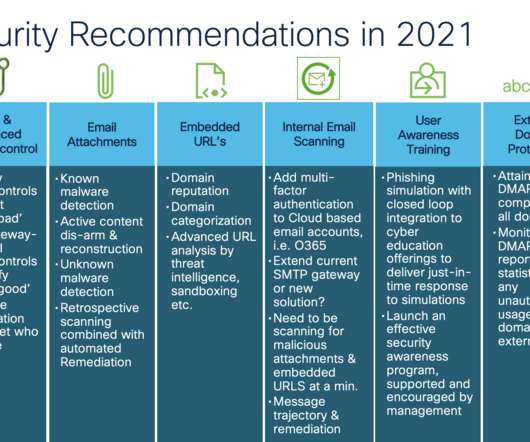
Now mix in architectural changes that support cloud productivity suites like Microsoft 365 and Google’s G-Suite to accelerate your business to cloud-based email security services. When it comes to safeguarding email against today’s advanced threats like phishing and malware information is power.

eSecurity Planet
AUGUST 30, 2023
A new Cloudflare phishing report notes that most of the 1 billion brand impersonation emails the company detected “passed” SPF, DKIM, and DMARC email authentication protocols. At the same time, an organization is also quite likely to fall for business email compromise and phishing attacks from their vendors.

SiteLock
AUGUST 27, 2021
Even a company with the most sophisticated cybersecurity tools and expert security teams can fall prey to cybercriminals if they overlook one area of vulnerability: their people. In fact, 97% of us can’t tell a phishing email from a legitimate one. Business Email Compromise (BEC) is similar to phishing. billion.

eSecurity Planet
AUGUST 3, 2023
None of these security best practices are new, but increasingly sophisticated adversaries make it more important than ever to get them right. None of these security best practices are new, but increasingly sophisticated adversaries make it more important than ever to get them right.

eSecurity Planet
SEPTEMBER 9, 2022
The most common types of attacks were cloud compromise, ransomware, supply chain , and business email compromise (BEC)/ spoofing / phishing. Healthcare Security Defenses. Two of the more common healthcare cybersecurity defenses the report found are training and awareness programs and employee monitoring.

The Last Watchdog
NOVEMBER 1, 2023
Cybersecurity Training and Phishing Testing: The easiest part of a system to hack is the human being. The only way to prevent this part of your defense is through training and testing. Help your employees become better defenders of your data.

eSecurity Planet
DECEMBER 10, 2023
This can be done through a variety of attacks, such as spear phishing , and may require the attacker to steal multiple sets of credentials before they reach the information they need. Computer systems and networks that use default or factory credentials for servers and applications are more susceptible to this kind of attack.

IT Security Guru
DECEMBER 15, 2022
By shifting security professionals’ mindset from a disparate, tool-based approach to a platform approach, businesses can improve their identity security defenses to protect against the modern threat landscape.” .

Hacker Combat
APRIL 6, 2022
The best ransomware protection combines solid, layered security defenses with data backups that an attacker can’t encrypt. Being Wary of Phishing Emails. Be on the lookout for phishing emails that appear to come from legitimate companies or individuals. Regular Software Updates.

Security Affairs
MAY 21, 2020
The company is investigating the incident and announced that it is taking action to strengthen its security defenses and prevent similar incidents in the future. Home Chef users should remain vigilant against phishing attacks and suspicious activity in their accounts. Subscription”).

eSecurity Planet
OCTOBER 11, 2023
“This is typically achieved through social engineering attacks with spear phishing to gain initial access to a host before searching for other internal vulnerable targets. Just because your Exchange Server doesn’t have internet-facing authentication doesn’t mean it’s protected.”
eSecurity Planet
AUGUST 23, 2021
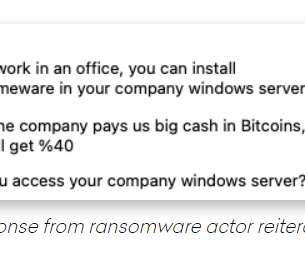
The bad actor told Hassold that he initially sent senior-level executives at the targeted companies phishing emails in hopes of compromising their accounts, but after that failed, he turned to trying to lure employees to unleash the ransomware themselves. Threat Traced to Nigeria. But this is just the start.”.
Security Affairs
NOVEMBER 3, 2022
It focused on deploying POS malware and launching targeted spear-phishing attacks against organizations worldwide. In order to weaken the security defenses installed on the target machine, Black Basta targets installed security solutions with specific batch scripts downloaded into the Windows directory.

Malwarebytes
MARCH 5, 2021
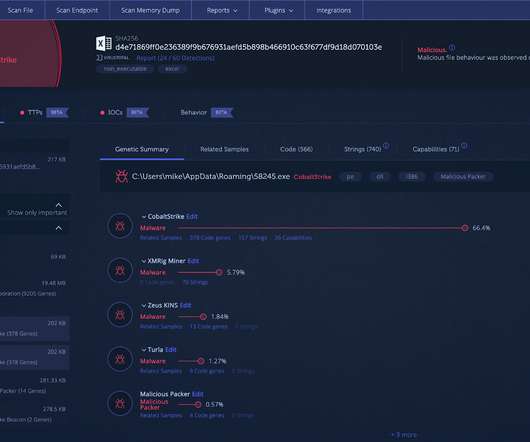
Threat actors often vary their techniques to thwart security defenses and increase the efficiency of their attacks. Researchers found several actors that have exploited this conflict via phishing lures to drop AgentTesla and PoetRat. This blog post was authored by Hossein Jazi. C2: vnedoprym.kozow[.]com com 111.90.150[.]37.

Duo's Security Blog
JULY 27, 2023
" Organizations use this information to audit, assess, and implement security defense-in-depth strategies to mitigate cybersecurity attacks. MITRE ATT&CK is a "globally accessible knowledge base of adversary tactics and techniques based on real-world observations."

eSecurity Planet
JUNE 10, 2024
The fix: Improve email filtering to detect and prevent harmful attachments, and adopt strong endpoint security solutions. Regularly update anti-malware software and educate your personnel about phishing dangers.

CyberSecurity Insiders
MARCH 14, 2022
Taken together, this new Trends functionality allows security teams to quickly understand if a vulnerability is relevant to their organization, and to buy them the time they need to put security defenses in place. . . The new Trends Attack Visibility graph is included for members of the free GreyNoise community.

eSecurity Planet
FEBRUARY 26, 2024
The fix: Organizations may take a variety of preventive measures to reduce cybersecurity risks, such as increasing password complexity, segmenting networks, frequently updating software, enabling multifactor authentication, and raising awareness about phishing threats. CISA released a list of mitigations against LockBit’s activity.

eSecurity Planet
JANUARY 11, 2024
The US Cybersecurity and Infrastructure Security Agency (CISA) estimated that 90% of all successful attacks begin with phishing, which points at user’s devices instead of routers, IoT, and other types of unmanaged endpoints. Email Address By signing up to receive our newsletter, you agree to our Terms of Use and Privacy Policy.

SiteLock
AUGUST 27, 2021
Most simply don’t have the resources to employ a dedicated cybersecurity team or invest in comprehensive security awareness training, leaving employees more vulnerable to phishing attacks and other scams. That means you need to have a plan for responding to attacks that break through even the most secure defenses.
eSecurity Planet
MARCH 14, 2022
Pentesting involves vulnerability exploitation and post-exploitation actions – the idea is to conduct a real attack, like cybercriminals would do, except with an explicit authorization from the company in order to identify weaknesses and improve security defenses.
eSecurity Planet
MARCH 15, 2024
It also teaches users about social engineering, phishing , and brute force attacks. Vulnerability assessment: HackerGPT makes it easier to analyze vulnerabilities by offering instructions on how to discover, prioritize, and mitigate security flaws.

SC Magazine
APRIL 7, 2021
While AI increasingly gets used to automate repetitive tasks, improve security and identify vulnerabilities, hackers will in turn build their own ML tools to target these processes. Secure and manage AI to prevent malfunctions.

eSecurity Planet
APRIL 1, 2024
out of 10), allowed successful phishing attacks to initiate a browser request for command safeguards bypass in the Splunk Enterprise and Splunk Cloud Platform Dashboard Examples Hub. The largest number of updates address third-party updates in Splunk Enterprise and Universal Forwarder that range between high and low in severity.

eSecurity Planet
AUGUST 22, 2023
Regular Security Audits: Security audits using vulnerability scans or penetration tests should be conducted regularly to detect vulnerabilities and verify that security rules are properly implemented and followed. Email Address By signing up to receive our newsletter, you agree to our Terms of Use and Privacy Policy.

eSecurity Planet
AUGUST 25, 2021
” Zero trust is a critical tool in the security defense arsenal, especially as more companies shift to a fully remote or hybrid work environment. Social engineering attacks like phishing, scareware, and deep fakes are frequent tactics hackers use to gain access to your business systems from the inside.

Security Boulevard
JULY 7, 2023
Delve into the multi-stage attack methodology, from deceptive phishing emails to custom-built modules, as we dissect its techniques and shed light on its impact. Gain valuable insights into the evolving threat landscape and learn how organizations can fortify their defenses against this emerging Latin American cyber threat.

eSecurity Planet
OCTOBER 31, 2023
Social Engineering or Phishing Test Report: The Volkis phishing campaign report provides good process details, but lacks graphical representation of the findings to reinforce easy understanding of the executive summary. Email Address By signing up to receive our newsletter, you agree to our Terms of Use and Privacy Policy.

CyberSecurity Insiders
MAY 16, 2022
That investment requires shifting attitudes from general awareness of security, which most workers already have, to genuinely caring about it and seeing themselves as a true part of their company’s security defenses. Reviewing best practices in a creative way is good, but security programs and training should go beyond this.

eSecurity Planet
OCTOBER 6, 2023
Despite all the advances in cybersecurity, email remains the starting point for the vast majority of cyberattacks, as phishing, malware and social engineering remain effective attack techniques. That makes email security software a worthwhile investment for organizations of all sizes. The Complete Protect plan, which costs $6.00

eSecurity Planet
NOVEMBER 10, 2023
What Are DNS Security Extensions (DNSSEC)? After all, with most processes now touching the internet, a secure DNS solution can block threats beyond DNS processes and help secure email, endpoints, remote users, and more. Email Address By signing up to receive our newsletter, you agree to our Terms of Use and Privacy Policy.

Thales Cloud Protection & Licensing
OCTOBER 24, 2019
Digital attackers can use malicious website and phishing accounts to trick users into handing over their password and, by extension, they key to their account. That’s why security professionals need to take additional steps to safeguard employees’ accounts. Implement Multi-Factor Authentication. Employ Device Encryption.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content