Cybercrime group FIN7 targets Veeam backup servers
CSO Magazine
APRIL 28, 2023
Researchers warn that a financially motivated cybercrime group known as FIN7 is compromising Veeam Backup & Replication servers and deploying malware on them.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

CSO Magazine
APRIL 28, 2023
Researchers warn that a financially motivated cybercrime group known as FIN7 is compromising Veeam Backup & Replication servers and deploying malware on them.
Security Affairs
SEPTEMBER 2, 2022
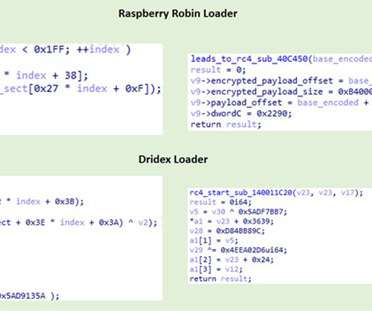
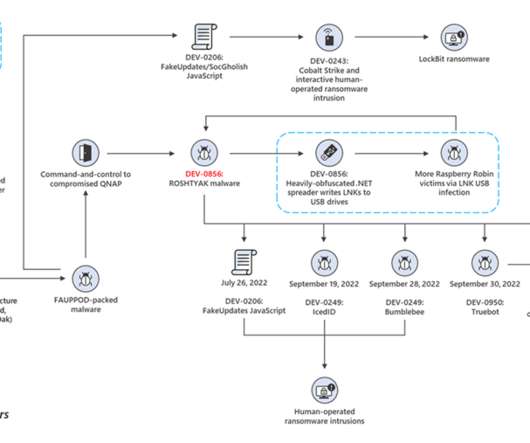
Researchers attribute the Raspberry Robin malware to the Russian cybercrime group known as Evil Corp group. IBM Security X-Force researchers discovered similarities between a component used in the Raspberry Robin malware and a Dridex malware loader, which was part of the malicious operations of the cybercrime gang Evil Corp.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
Security Affairs
JUNE 16, 2023
An updated version of the Android remote access trojan GravityRAT can steal WhatsApp backup files and can delete files ESET researchers discovered an updated version of Android GravityRAT spyware that steals WhatsApp backup files and can delete files. The malware is distributed as the messaging apps BingeChat and Chatico.

Malwarebytes
SEPTEMBER 15, 2023
The report follows the Internet Organized Crime Assessment (IOCTA), Europol’s assessment of the cybercrime landscape and how it has changed over the last 24 months. These groups work closely with other malware-as-a-service groups to compromise high-revenue targets and post huge ransom demands, running into millions of Euros.
Krebs on Security
AUGUST 2, 2022
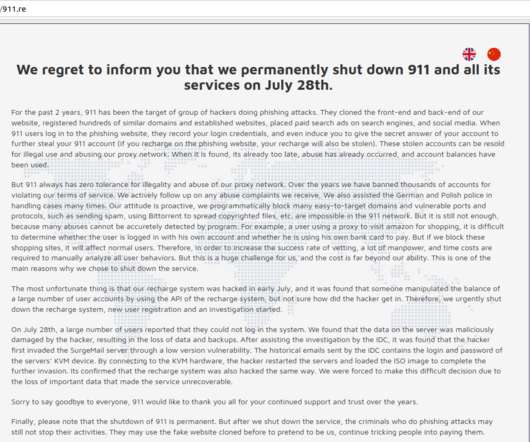
Compounding the problem, several remaining malware-based proxy services have chosen to block new registrations to avoid swamping their networks with a sudden influx of customers. re abruptly announced it was permanently closing after a cybersecurity breach allowed unknown intruders to trash its servers and delete customer data and backups.
Security Affairs
OCTOBER 22, 2021
FIN7 is a Russian criminal group that has been active since mid-2015, it focuses on restaurants, gambling, and hospitality industries in the US to harvest financial information that was used in attacks or sold in cybercrime marketplaces. Once gained access to the target network, the threat actors could then drop malware and ransomware. .
Security Affairs
DECEMBER 24, 2022
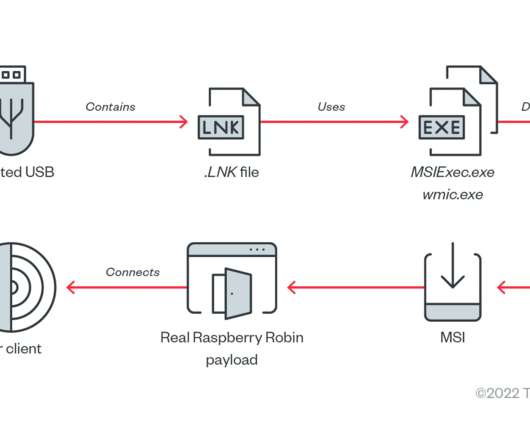
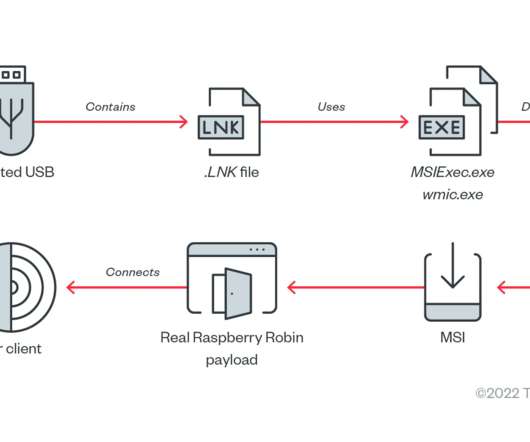
“We found samples of the Raspberry Robin malware spreading in telecommunications and government office systems beginning September.” ” Raspberry Robin is a Windows worm discovered by cybersecurity researchers from Red Canary, the malware propagates through removable USB devices. .” exe, and rundll32.exe.

Security Affairs
JANUARY 13, 2024
The Finish National Cybersecurity Center (NCSC-FI) warns of increased Akira ransomware attacks targeting NAS and tape backup devices of organizations in the country. Threat actors are wiping NAS and backup devices. In addition, during Christmas, there was one incident caused by another ransomware malware family.”

SiteLock
AUGUST 27, 2021
As cybercrime grows and evolves, malware remains a constant weapon in a cybercriminal’s armory. Malware, short for malicious software, is created with the intent of causing harm to a website or computer. In many cases, victims of malware may not realize they’ve been attacked until it’s too late.

Adam Levin
NOVEMBER 6, 2020
In a joint cybersecurity advisory with the Cybersecurity and Infrastructure Agency (CISA) and the Department of Health and Human Services (HHS), the FBI warned of an “increased and imminent cybercrime threat to U.S. Using air-gapped and password protected backups. hospitals and healthcare providers.”. Using multi factor authentication.

Security Affairs
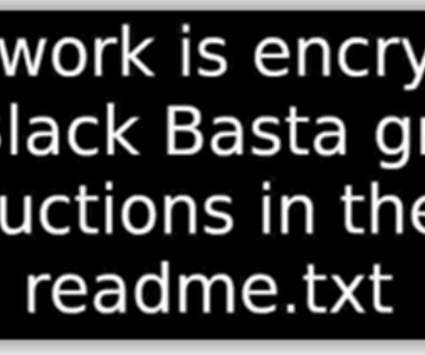
MAY 12, 2024
Some of the victims’ ransom payments were sent by both Conti and Black Basta groups to the gang behind the Qakbot malware. Follow me on Twitter: @securityaffairs and Facebook and Mastodon Pierluigi Paganini ( SecurityAffairs – hacking, cybercrime) 61,9% of the victims are in the US, 15.8% in Germany, and 5.9%

Security Affairs
JANUARY 13, 2024
The Finish National Cybersecurity Center (NCSC-FI) warns of increased Akira ransomware attacks targeting NAS and tape backup devices of organizations in the country. Threat actors are wiping NAS and backup devices. According to the NCSC-FI, six out of seven infections were caused by Akira family malware. concludes the alert.
Security Affairs
JULY 29, 2022
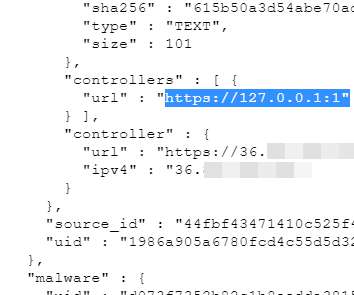
Microsoft linked the recently discovered Raspberry Robin Windows malware to the notorious Evil Corp operation. On July 26, 2022, Microsoft researchers discovered that the FakeUpdates malware was being distributed via Raspberry Robin malware. The malware uses TOR exit nodes as a backup C2 infrastructure.
Krebs on Security
DECEMBER 8, 2022
.” While CLOP as a money making collective is a fairly young organization, security experts say CLOP members hail from a group of Threat Actors (TA) known as “TA505,” which MITRE’s ATT&CK database says is a financially motivated cybercrime group that has been active since at least 2014. ” . ”

SecureWorld News
FEBRUARY 28, 2024
By co-opting the ransomware group's own communication channels, police aimed to sow doubts in the cybercrime community reliant on LockBit's tools and services. However, it claimed critical systems like ransom payment tracking remained unaffected due to backups. Nonetheless.

Krebs on Security
JANUARY 8, 2024
In 2020, the United States brought charges against four men accused of building a bulletproof hosting empire that once dominated the Russian cybercrime industry and supported multiple organized cybercrime groups. From January 2005 to April 2013, there were two primary administrators of the cybercrime forum Spamdot (a.k.a
Security Affairs
DECEMBER 24, 2022
“We found samples of the Raspberry Robin malware spreading in telecommunications and government office systems beginning September.” ” Raspberry Robin is a Windows worm discovered by cybersecurity researchers from Red Canary, the malware propagates through removable USB devices. .” exe, and rundll32.exe.

SecureWorld News
AUGUST 8, 2022
Cybersecurity and Infrastructure Security Agency (CISA) and the Australian Cyber Security Centre (ACSC) released a joint Cybersecurity Advisory (CSA) providing details on the top malware strains of 2021. The top malware strains in 2021 included remote access Trojans (RATs), banking Trojans, information stealers, and ransomware.

Malwarebytes
SEPTEMBER 19, 2023
Since then, cybercrime group specialists from the North Rhine-Westphalia State Criminal Police Office (LKA NRW), together with the Cybercrime Central and Contact Point (ZAC NRW), carried out another targeted strike against people associated with the criminal network. Create offsite, offline backups. Prevent intrusions.

Security Affairs
OCTOBER 31, 2022
The infection chain was divided into four stages : The malware was installed through a dropper, a program executed by opening an attachment to a deceptive e-mail, probably a fake pdf or doc file, or executed directly from the Internet, without user interaction, exploiting the exploit described in the point 4. The infection chain.
Security Affairs
APRIL 9, 2023
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you in your email box. billion rubles.

Malwarebytes
JULY 8, 2022
One of the biggest problems in the cybercrime section of the report relates to backups. Specifically: The lack of backups when dealing with hacking incidents. Backups in Brazil: An uphill struggle. Backups are an essential backstop that can help against several forms of attack, as well as mistakes and mishaps.
Security Affairs
JUNE 17, 2023
Margaret’s Health is the first hospital to cite a cyberattack as a reason for its closure A database containing data of +8.9 Margaret’s Health is the first hospital to cite a cyberattack as a reason for its closure A database containing data of +8.9
Krebs on Security
JUNE 2, 2020
Over the past 24 hours, the crooks responsible for spreading the ransom malware “REvil” (a.k.a. “Others have gotten the message about the need for good backups, and probably don’t need to pay. .” It may be worth hiring a competent security firm to make sure this is done right.
Krebs on Security
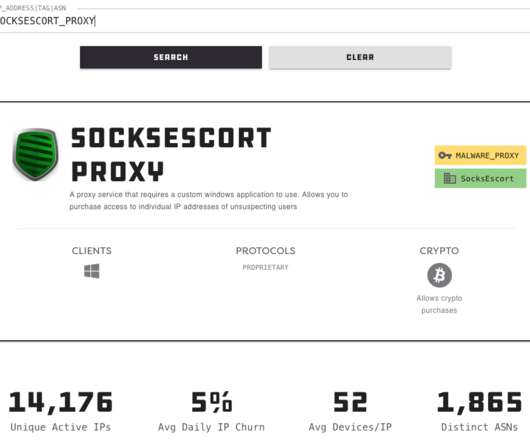
JULY 29, 2022
These services can be used in a legitimate manner for several business purposes — such as price comparisons or sales intelligence — but they are massively abused for hiding cybercrime activity because they can make it difficult to trace malicious traffic to its original source. re servers, data and backups of that data.

SecureWorld News
JANUARY 19, 2023
The exclusive webcast covers: • What's happening in the ransomware realm right now • Three tips from the cybercriminals themselves • Conti cybercrime group insights Register to view the webcast on-demand at your convenience and earn 1 CPE credit in the process. It will be available for viewing through August 2023.

Malwarebytes
JANUARY 25, 2024
In how far new moves on the front of a United Nations Cybercrime Treaty will have a short-term effect on the behavior of state-sponsored groups is very hard to predict. But the NCSC does expect AI to play a larger role in the near future when it comes to the development of malware and exploits. Create offsite, offline backups.

Malwarebytes
FEBRUARY 14, 2024
The potential riches are enormous and there’s no other form of cybercrime that’s so lucrative, so why aren’t we seeing more attacks? To learn more about how big game ransomware is evolving, the threat of zero-day ransomware, and how to protect against them, read our 2024 State of Malware report. READ THE REPORT
Security Affairs
JULY 2, 2023
Illicit Telegram Communities Dismantling of an encrypted network sends shockwaves through organised crime groups across Europe TSMC Says Supplier Hacked After Ransomware Group Claims Attack on Chip Giant Malware Trojanized Super Mario Game Installer Spreads SupremeBot Malware Initial research exposing JOKERSPY Who is 8BASE?
IT Security Guru
NOVEMBER 20, 2023
From protecting sensitive corporate data to safeguarding our personal information, the battle against cybercrime is ongoing. They urgently insist on immediate action, which typically involves payment or granting remote access to the victim’s device, only to introduce malware or steal data.

Spinone
DECEMBER 17, 2018
G Suite for Education backup and security should be taken seriously as GSFE (formerly known as Google Apps for Education) puts creative, nimble, and flexible learning at the center of the educational experience. How to Ensure G Suite for Education Backup and Security? What is Google G Suite for Education (GSFE)?
Krebs on Security
OCTOBER 2, 2020
Over the past 10 days, someone has been launching a series of coordinated attacks designed to disrupt Trickbot , an enormous collection of more than two million malware-infected Windows PCs that are constantly being harvested for financial data and are often used as the entry point for deploying ransomware within compromised organizations.

Krebs on Security
SEPTEMBER 30, 2023
.” New York City-based cyber intelligence firm Flashpoint said the Snatch ransomware group was created in 2018, based on Truniger’s recruitment both on Russian language cybercrime forums and public Russian programming boards. “Experience in backup, increase privileges, mikicatz, network.

Security Affairs
APRIL 5, 2019
Researchers at AT&T Alien Labs have spotted a malware called Xwo that is actively scanning the Internet for exposed web services and default passwords. Experts at AT&T Alien Labs discovered a new piece of malware called Xwo that is actively scanning the Internet for exposed web services and default passwords. Www backup paths.
Security Affairs
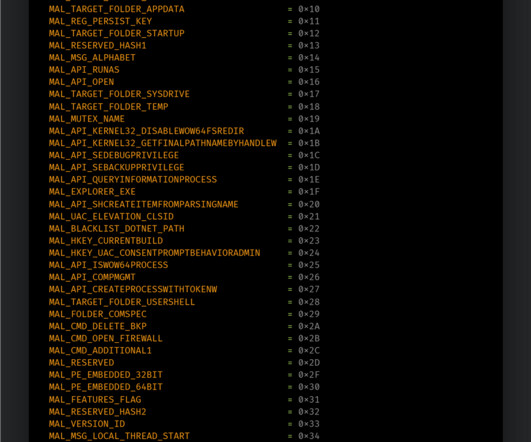
NOVEMBER 19, 2023
The Talos researchers discovered a number of features implemented by Phobos allowing operators to establish persistence in a targeted system, perform speedy encryption, and remove backups. Disable system recovery, backup and shadow copies and the Windows firewall. Embedded configuration with more than 70 options available.

Webroot
NOVEMBER 8, 2021
Afterall, the dark web is where most cybercrimes get their start. In fact, the rising rates of malware and computer viruses can partially be explained by cyber criminals coming together to pool their talent. They’ve created a new model for cybercrime where criminal specialists sell their talents to the highest bidder.

Security Affairs
NOVEMBER 6, 2022
Cisco addressed several high-severity flaws in its products LockBit ransomware gang claims the hack of Continental automotive group 250+ U.S. Cisco addressed several high-severity flaws in its products LockBit ransomware gang claims the hack of Continental automotive group 250+ U.S.

CyberSecurity Insiders
JUNE 13, 2023
Stay informed about the latest cyber threats, such as phishing, malware, ransomware, and social engineering attacks. Be Skeptical of Phishing Attempts: Phishing is a prevalent cybercrime technique that involves tricking individuals into divulging their sensitive information.
McAfee
OCTOBER 31, 2021
By getting an executive on the hook, they could potentially convince them to download a job spec that is malware. Unfortunately, cybercrime has nonrepudiation and threat actors can deny all knowledge and get away with it. Techniques & Tactics. Prevention. It’s important to understand the threat and what is happening.
Security Affairs
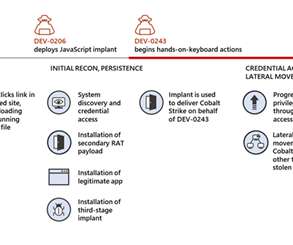
OCTOBER 27, 2022
In October 2022, the malware was used in post-compromise activity attributed to another actor, DEV-0950 (which overlaps with FIN11 / TA505 cybercrime gang). In some cases, the attackers delivered the Truebot malware between the Raspberry Robin infection and the Cobalt Strike deployment.

SiteLock
AUGUST 27, 2021
In fact, the World Economic Forum (WEF) projects that by 2021: Global cybercrime costs could total approximately $6 trillion in the US. If cybercrime were a country, it would have the third largest economy in the world. Clearly, cybercrime is big business, and it operates like one. How big is the impact of cybercrime?

Security Affairs
NOVEMBER 8, 2023
To be prepared for cyber incidents, organizations should maintain offline backups of data, and regularly maintain backup and restoration, ensure all backup data is encrypted, immutable and cover the entire organization’s data infrastructure, and ensure their backup data is not already infected.

Security Affairs
OCTOBER 29, 2021
Pundari also added that the government didn’t pay a ransom to the threat actors and the system was recovered from backups. Therefore restoration of services to all government agencies, including the sub-national level, will be done gradually, so as not to compromise or allow any further spread of this malware or other virus.”
Security Affairs
JUNE 7, 2022
The QBot malware operation has partnered with Black Basta ransomware group to target organizations worldwide. Researchers from NCC Group spotted a new partnership in the threat landscape between the Black Basta ransomware group and the QBot malware operation.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content