How can small businesses ensure Cybersecurity?
CyberSecurity Insiders
JUNE 7, 2023
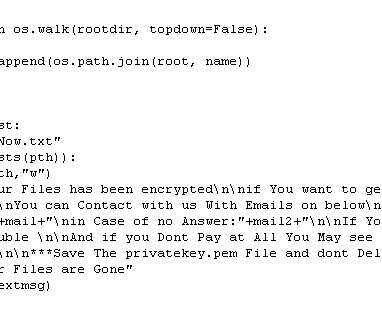
Therefore, it’s crucial that small businesses make cybersecurity a top priority. What drives more cybersecurity attacks on small businesses? The influx of remote working culture has added new challenges and cybersecurity risks for small businesses. They also have a limited budget to spend on effective cyber security measures.

















Let's personalize your content