Brexit Deal Mandates Old Insecure Crypto Algorithms
Schneier on Security
DECEMBER 31, 2020
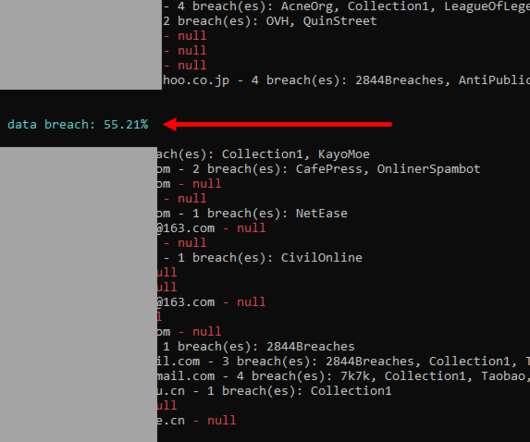
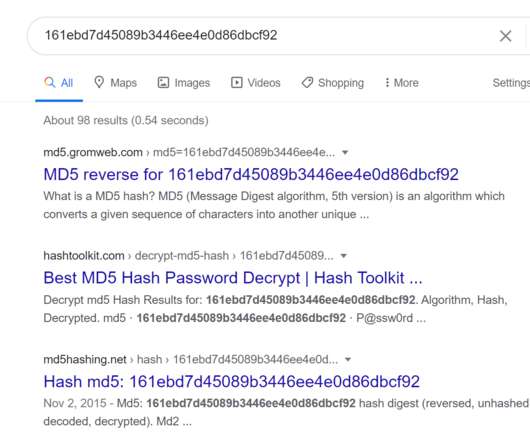
In what is surely an unthinking cut-and-paste issue, page 921 of the Brexit deal mandates the use of SHA-1 and 1024-bit RSA: The open standard s/MIME as extension to de facto e-mail standard SMTP will be deployed to encrypt messages containing DNA profile information. The protocol s/MIME (V3) allows signed receipts, security labels, and secure mailing lists… The underlying certificate used by s/MIME mechanism has to be in compliance with X.509 standard… The processing rules for s/MIM




















Let's personalize your content