Cisco Secure: Supporting NIST Cybersecurity Framework
Cisco Security
JUNE 18, 2021
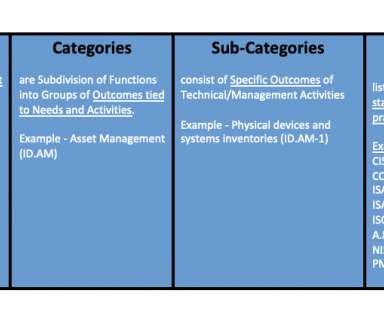
While many organizations are challenged with managing and improving their cybersecurity programs against the dynamic threat landscape, it’s not easy to pick one framework over another. National Institute of Standards and Technology (NIST) developed the Cybersecurity Framework (CSF) exactly for this reason. ISO27000 series?











Let's personalize your content