Russia-linked APT28 targets govt bodies with fake NATO training docs
Security Affairs
SEPTEMBER 23, 2020
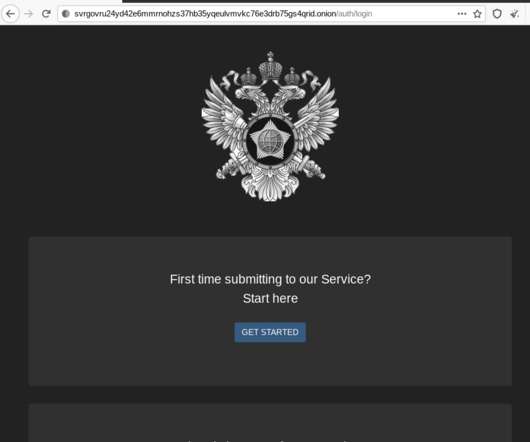
Even today, less than half of the known antivirus engines are flagging the infection on VirusTotal , as observed by BleepingComputer: The APT28 group (aka Fancy Bear , Pawn Storm , Sofacy Group , Sednit , and STRONTIUM ) has been active since at least 2007 and it has targeted governments, militaries, and security organizations worldwide.















Let's personalize your content