Financially motivated Earth Lusca threat actors targets organizations worldwide
Security Affairs
JANUARY 18, 2022
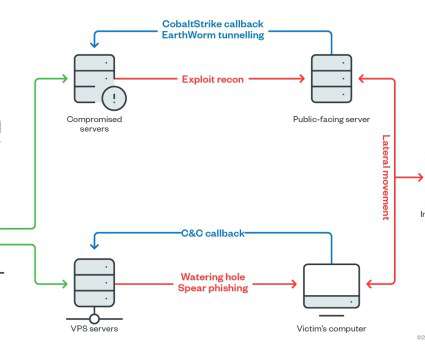
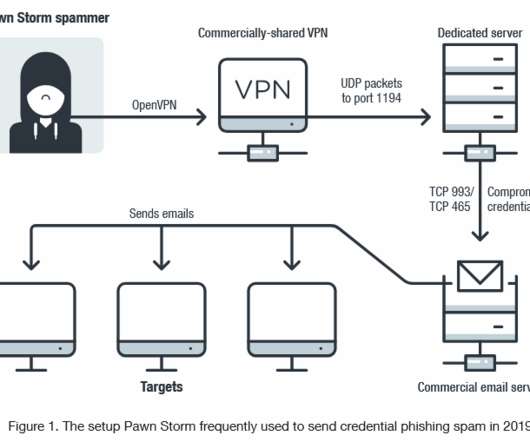
Trend Micro researchers spotted an elusive threat actor, called Earth Lusca, that targets organizations worldwide via spear-phishing and watering hole attacks. . The Winnti group was first spotted by Kaspersky in 2013, but according to the researchers the gang has been active since 2007. Both clusters served as a C&C server.











Let's personalize your content