Ten Years Later, New Clues in the Target Breach
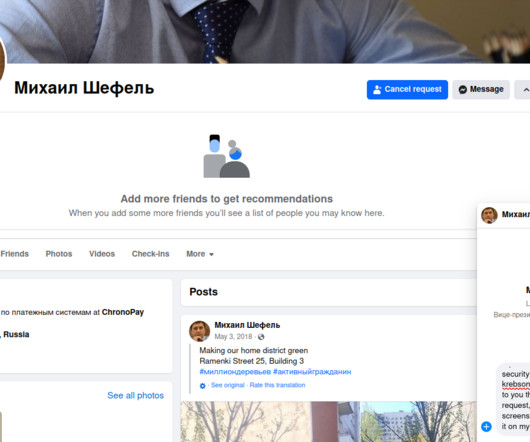
Krebs on Security
DECEMBER 14, 2023
The malware used in the Target breach included the text string “ Rescator ,” which also was the handle chosen by the cybercriminal who was selling all of the cards stolen from Target customers. For starters, the text string “Rescator” was found in some of the malware used in the Target breach.















Let's personalize your content