New Ttint IoT botnet exploits two zero-days in Tenda routers
Security Affairs
OCTOBER 5, 2020
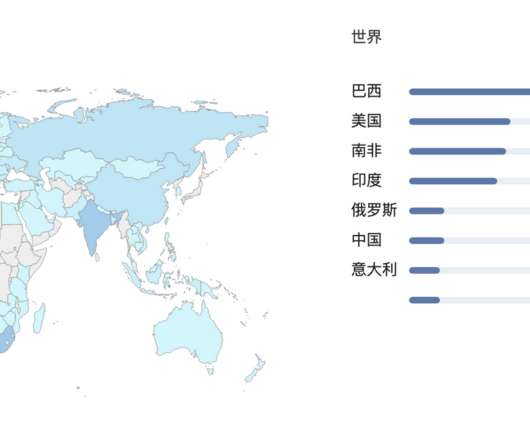
Security researchers provided technical details about an IoT botnet dubbed Ttint that has been exploiting two zero-days in Tenda routers. Security researchers at Netlab, the network security division Qihoo 360, have published a report that details an IoT botnet dubbed Ttint. Pierluigi Paganini.














Let's personalize your content