Cybercrime gang FIN7 returned and was spotted delivering Clop ransomware
Security Affairs
MAY 20, 2023
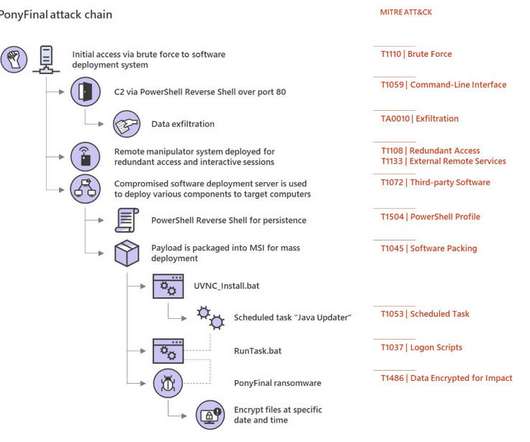
Cybercriminal gang FIN7 returned with a new wave of attacks aimed at deploying the Clop ransomware on victims’ networks. The group was spotted deploying the Clop ransomware in opportunistic attacks in April 2023. Then they use OpenSSH and Impacket to move laterally and deploy the Clop ransomware payload.












Let's personalize your content