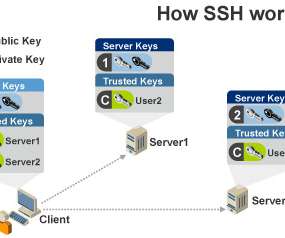
How Secure Shell (SSH) Keys Work
Security Boulevard
AUGUST 5, 2022
SSH authenticates the parties involved and allows them to exchange commands and output via multiple data manipulation techniques. Once the parties have played an equal role in generating the shared secret key, they must authenticate themselves. The most common means of authentication is via SSH asymmetric key pairs. 17965 views.











Let's personalize your content