Overview of IoT threats in 2023
SecureList
SEPTEMBER 21, 2023
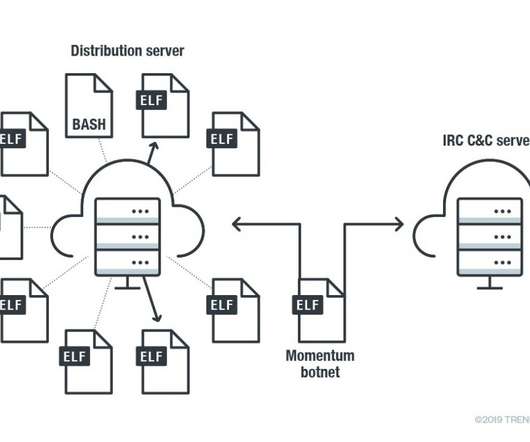
As if that were not enough, many IoT devices have unalterable main passwords set by manufacturers. Dark web services: DDoS attacks, botnets, and zero-day IoT vulnerabilities Of all IoT-related services offered on the dark web, DDoS attacks are worth examining first. Unfortunately, users tend to leave these passwords unchanged.












Let's personalize your content