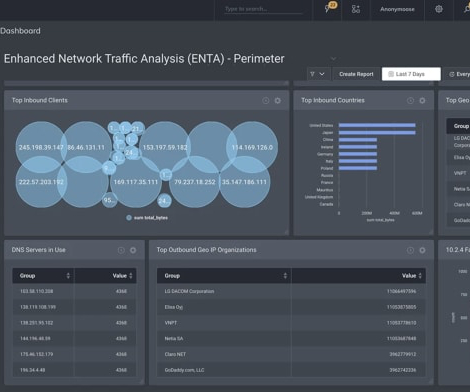
GUEST ESSAY: How SIEMS, UEBAs fall short in today’s turbulent threat landscape
The Last Watchdog
JULY 30, 2018
Related article: SIEMs strive for a comeback. The painful impact of cyber attacks on businesses is worsening despite advances in technology aimed at protecting enterprises from malicious network traffic, insider threats, malware, denial of service attacks and phishing campaigns.












Let's personalize your content