How Thales and Red Hat Protect Telcos from API Attacks
Thales Cloud Protection & Licensing
FEBRUARY 21, 2024
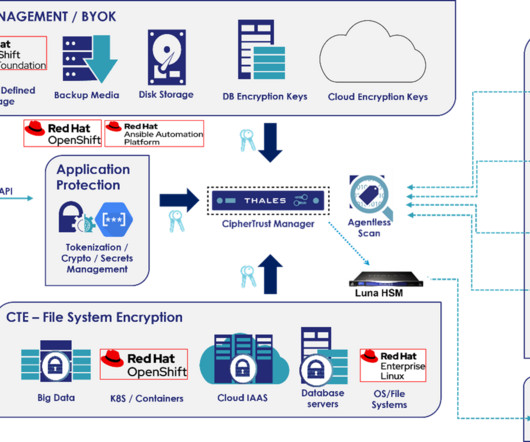
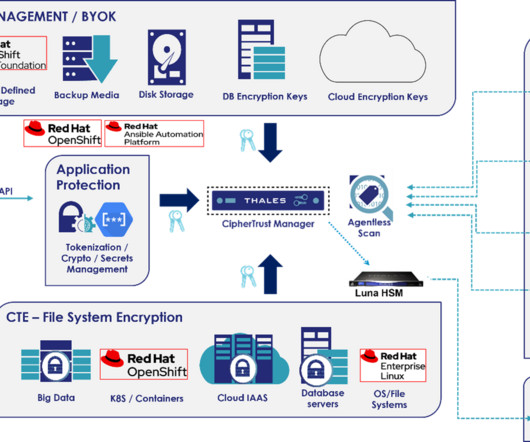
In this blog, we will explain the unique data security challenges for Telcos and three ways how both Thales and Red Hat can help them protect against future API attacks. Together, both Thales and Red Hat offer solutions to overcome some of these data protection and management challenges. What are APIs?








Let's personalize your content