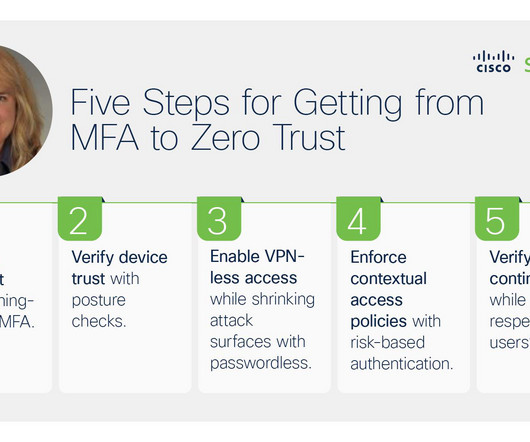
Charting a Course to Zero Trust Maturity: 5 Steps to Securing User Access to Apps
Duo's Security Blog
OCTOBER 6, 2023
Respect the user’s privacy and productivity by anonymizing location data and eliminating unnecessary decisions when continually verifying trust. .” – Jason Waits, Chief Information Security Officer (CISO), Inductive Automation Ready to start charting your zero trust program? ZTNA) – regardless of location or protocol.







Let's personalize your content