Combatting Deepfakes in Australia: Content Credentials is the Start
Tech Republic Security
MAY 8, 2024
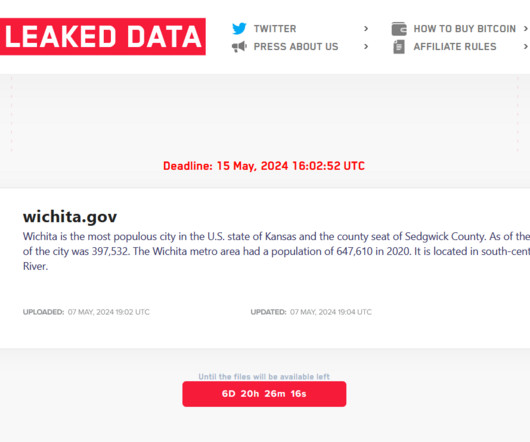
The production of deepfakes is accelerating at more than 1,500% in Australia, forcing organisations to create and adopt standards like Content Credentials.






























Let's personalize your content