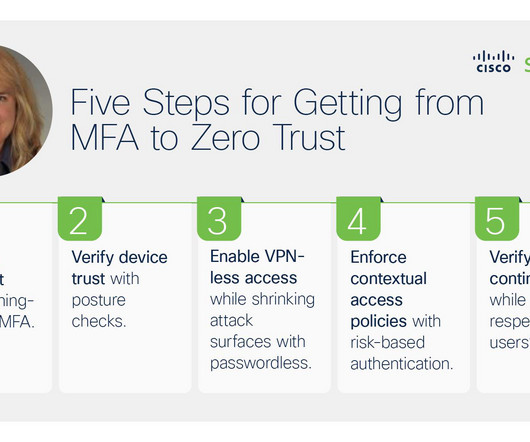
Charting a Course to Zero Trust Maturity: 5 Steps to Securing User Access to Apps
Duo's Security Blog
OCTOBER 6, 2023
In other words, it’s not just about implementing MFA to verify user trust, it’s about using phishing-resistant MFA with risk-based authentication , device posture checks and other security controls. TL,DR: Check out our on-demand webinar Your Zero Trust Roadmap , where we outline the five key steps to secure user access to apps.








Let's personalize your content