Water utility CISO offers tips to stay secure as IT and OT converge
SC Magazine
APRIL 26, 2021
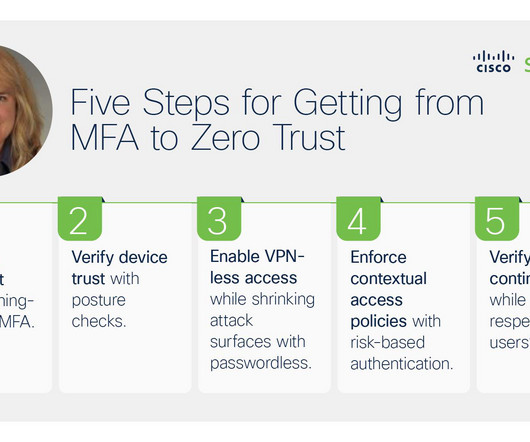
Kristin Sanders, CISO for the Albuquerque Bernalillo County Water Utility Authority, revealed how New Mexico’s largest water and wastewater utility has been addressing the security challenge. We’re able to roll that out not only for our desktop computers and for laptops and for VPN clients, but even for mobile devices,” said Sanders. “So









Let's personalize your content