Frequent VBA Macros used in Office Malware
Security Affairs
OCTOBER 1, 2019
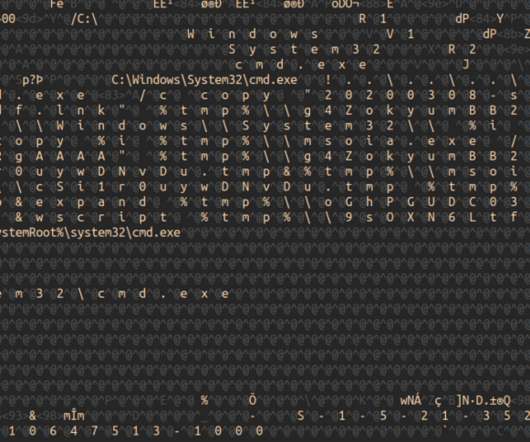
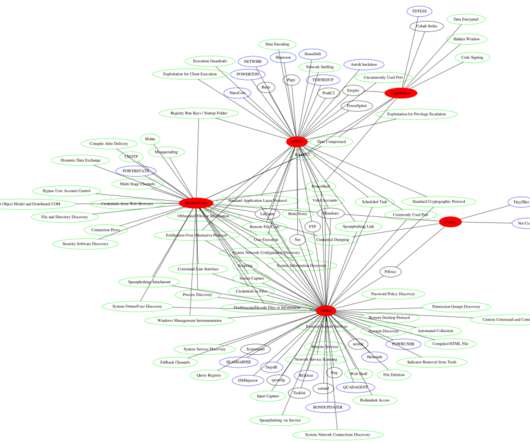
The malware expert Marco Ramilli collected a small set of VBA Macros widely re-used to “weaponize” Maldoc (Malware Document) in cyber attacks. Here comes the idea to collect a small set of VBA Macros widely re-used to “weaponize” Maldoc (Malware Document) in contemporary cyber attacks.












Let's personalize your content