The Evolving Role of Cyber Insurance in Mitigating Ransomware Attacks
SecureWorld News
MARCH 20, 2024
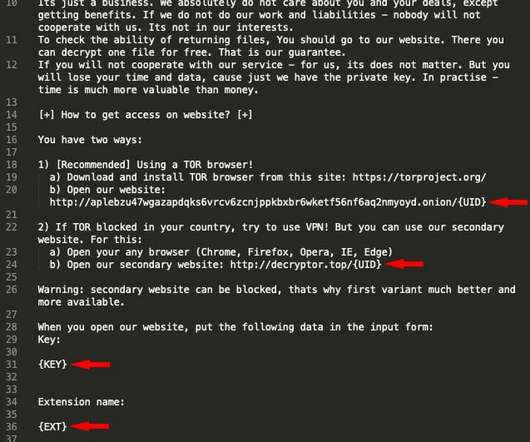
Ransomware attacks have become a significant threat to organizations of all kinds worldwide, with attackers encrypting data and demanding payment for its release. In this regard, many have touted cyber insurance as the knight in shining armor, the end all-be all in terms of mitigating criminals' assaults on your network.















Let's personalize your content