Google Chrome security tips for the paranoid at heart
Tech Republic Security
FEBRUARY 11, 2016
If you're a Google Chrome user who loses sleep about online privacy risks, check out these tricks to making your browsing experience more secure.

Tech Republic Security
FEBRUARY 11, 2016
If you're a Google Chrome user who loses sleep about online privacy risks, check out these tricks to making your browsing experience more secure.
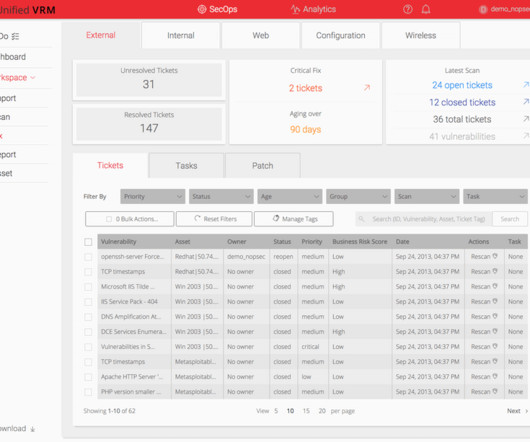
NopSec
FEBRUARY 17, 2016
Since product launch (2012), Unified VRM has been rapidly expanding with new features and advanced automation solutions for security professionals. By 2015, content inventory confirmed Unified VRM’s capabilities were outgrowing front-end visibility, so our team hit the drawing board to create a brand new information architecture that would maximize user’s ability to engage with impactful remediation.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
ForAllSecure
FEBRUARY 9, 2016
Although we have been very busy at ForAllSecure, we finally got the time to redo our website, huzzah! This website is a bit more pleasing on the eyes, and we hope to add more up-to-date information about our projects and what we're up to. Part of this refresh is also a new blog. We plan to talk about interesting things we are working on, so check back frequently!

Elie
FEBRUARY 10, 2016
Big data weaponization and malware-based espionage are usually associated with governments; however, they don’t own a monopoly on such activities. Also, online poker uses big data to profile user behavior. Players search for fish (bad players) and they use malware to spy on and rip off infected players at the (online) poker table. This blog post is a brief tour of some of the darkest aspects of online poker.

Advertisement
How many people would you trust with your house keys? Chances are, you have a handful of trusted friends and family members who have an emergency copy, but you definitely wouldn’t hand those out too freely. You have stuff that’s worth protecting—and the more people that have access to your belongings, the higher the odds that something will go missing.

Privacy and Cybersecurity Law
FEBRUARY 27, 2016
With the entry into force of the new Unterlassungsklagengesetz (UKlaG) [otherwise known as the “Gesetz zur Verbesserung der zivilrechtlichen Durchsetzung […].

Digital Shadows
FEBRUARY 1, 2016
On 26 January, Yuval Steinitz, the Israeli Minister of Infrastructure, Energy and Water Resources, announced to the 2016 CyberTech Conference. The post “Largest cyber attack” on Israel lacks power first appeared on Digital Shadows.
Cyber Security Informer brings together the best content for cyber security professionals from the widest variety of industry thought leaders.

ForAllSecure
FEBRUARY 9, 2016
Although we have been very busy at ForAllSecure, we finally got the time to redo our website, huzzah! This website is a bit more pleasing on the eyes, and we hope to add more up-to-date information about our projects and what we're up to. Part of this refresh is also a new blog. We plan to talk about interesting things we are working on, so check back frequently!

ForAllSecure
FEBRUARY 9, 2016
Although we have been very busy at ForAllSecure, we finally got the time to redo our website, huzzah! This website is a bit more pleasing on the eyes, and we hope to add more up-to-date information about our projects and what we're up to. Part of this refresh is also a new blog. We plan to talk about interesting things we are working on, so check back frequently!

Privacy and Cybersecurity Law
FEBRUARY 2, 2016
Today, political agreement has been reached on the new solution to replace the Safe Harbor regime, the so-called “EU-US Privacy […].

Privacy and Cybersecurity Law
FEBRUARY 1, 2016
‘Hot off the press’ as Commissioner Jourova continues to give her statement to the European Parliament: there is no deal […].

Advertiser: Revenera
In a recent study, IDC found that 64% of organizations said they were already using open source in software development with a further 25% planning to in the next year. Most organizations are unaware of just how much open-source code is used and underestimate their dependency on it. As enterprises grow the use of open-source software, they face a new challenge: understanding the scope of open-source software that's being used throughout the organization and the corresponding exposure.

Privacy and Cybersecurity Law
FEBRUARY 4, 2016
The Article 29 Working Party (WP 29) published their initial response to the new Privacy Shield yesterday. Here’s the good […].

ForAllSecure
FEBRUARY 9, 2016
In June, ForAllSecure participated in DARPA's Cyber Grand Challenge (CGC) Qualification Event (CQE) 1. During the event our automated system tweeted its progress, and to continue the trend of openness, we decided to publish a writeup of some more details about our system. Our team, Thanassis Avgerinos, David Brumley, John Davis, Ryan Goulden, Tyler Nighswander, and Alex Rebert spent many thousands of hours on our system, and now that the CQE is over, we're excited to give you a glimpse of its in

ForAllSecure
FEBRUARY 9, 2016
In June, ForAllSecure participated in DARPA's Cyber Grand Challenge (CGC) Qualification Event (CQE) 1. During the event our automated system tweeted its progress, and to continue the trend of openness, we decided to publish a writeup of some more details about our system. Our team, Thanassis Avgerinos, David Brumley, John Davis, Ryan Goulden, Tyler Nighswander, and Alex Rebert spent many thousands of hours on our system, and now that the CQE is over, we're excited to give you a glimpse of its in

ForAllSecure
FEBRUARY 9, 2016
In June, ForAllSecure participated in DARPA's Cyber Grand Challenge (CGC) Qualification Event (CQE) 1. During the event our automated system tweeted its progress, and to continue the trend of openness, we decided to publish a writeup of some more details about our system. Our team, Thanassis Avgerinos, David Brumley, John Davis, Ryan Goulden, Tyler Nighswander, and Alex Rebert spent many thousands of hours on our system, and now that the CQE is over, we're excited to give you a glimpse of its in

Advertisement
The healthcare industry has massively adopted web tracking tools, including pixels and trackers. Tracking tools on user-authenticated and unauthenticated web pages can access personal health information (PHI) such as IP addresses, medical record numbers, home and email addresses, appointment dates, or other info provided by users on pages and thus can violate HIPAA Rules that govern the Use of Online Tracking Technologies by HIPAA Covered Entities and Business Associates.
Let's personalize your content