Australia Stresses Cybersecurity Precautions in Wake of Ukraine Conflict
Duo's Security Blog
MARCH 9, 2022
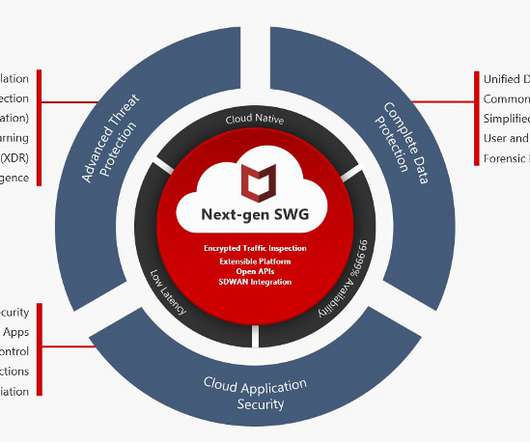
Firewall status, drive encryption status, password status and whether an antivirus or anti-malware agent is running can all contribute to improved security resilience. Adding multi-factor authentication to your virtual private network (VPN) can increase protection against credential theft.











Let's personalize your content