10 Top Open Source Penetration Testing Tools
eSecurity Planet
FEBRUARY 24, 2022
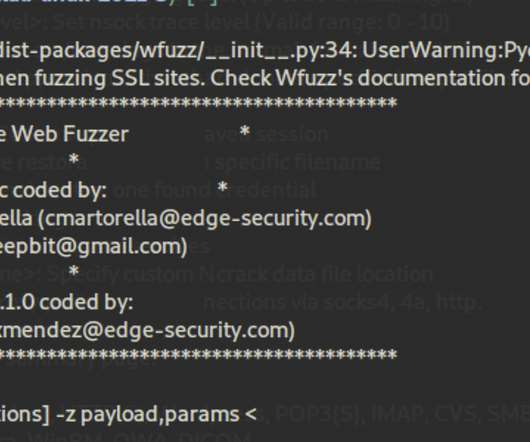
Here we’re focusing on some lesser-known but still worthy open-source solutions that can be used separately for specific purposes or combined to run comprehensive penetration tests. The Open Web Application Security Project (OWASP) is a nonprofit foundation and an open community dedicated to security awareness.















Let's personalize your content