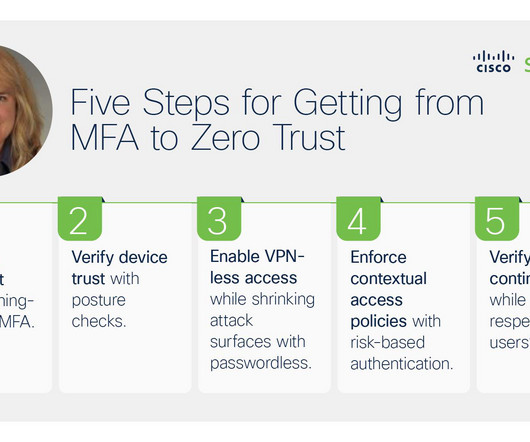
Charting a Course to Zero Trust Maturity: 5 Steps to Securing User Access to Apps
Duo's Security Blog
OCTOBER 6, 2023
To achieve more resilience in this heightened risk environment, stepping up zero trust maturity is essential. In other words, it’s not just about implementing MFA to verify user trust, it’s about using phishing-resistant MFA with risk-based authentication , device posture checks and other security controls.








Let's personalize your content