Ignore the Insider Threat at Your Peril
Dark Reading
APRIL 8, 2019
Attacks from insiders often go undiscovered for months or years, so the potential impact can be huge. These 11 countermeasures can mitigate the damage.

 insider-threats ignore-the-insider-threat-at-your-peril
insider-threats ignore-the-insider-threat-at-your-peril 
Dark Reading
APRIL 8, 2019
Attacks from insiders often go undiscovered for months or years, so the potential impact can be huge. These 11 countermeasures can mitigate the damage.
Anton on Security
SEPTEMBER 14, 2022
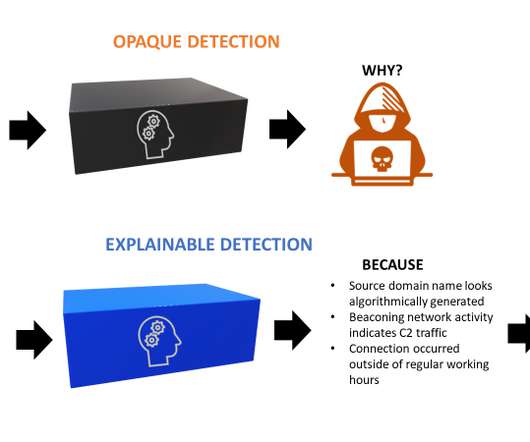
When we detect threats we expect to know what we are detecting. But as we increasingly move towards more elaborate detection approaches like detection-as-code using languages like the Sigma language , or Python, it is becoming more difficult to deduce in detail how certain threat detections work. Sounds painfully obvious, right?

Malwarebytes
APRIL 14, 2021
They allow attackers to access and creep around inside the compromised networks. Some organisations missed or ignored the mass-massaging about the threat. We’ll get to that but before we do, let’s talk about the perils of getting involved in situations. Bizarrely, they did this without letting the admins know beforehand.
Let's personalize your content