No SOCKS, No Shoes, No Malware Proxy Services!
Krebs on Security
AUGUST 2, 2022
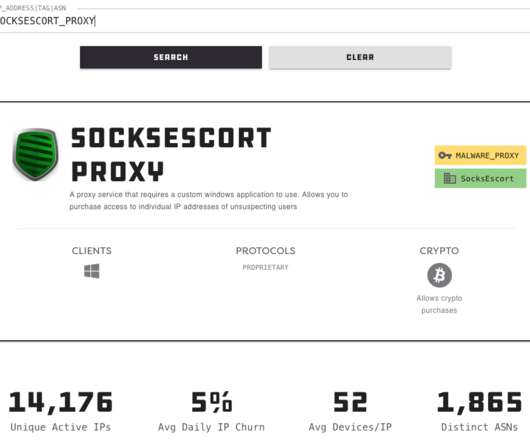
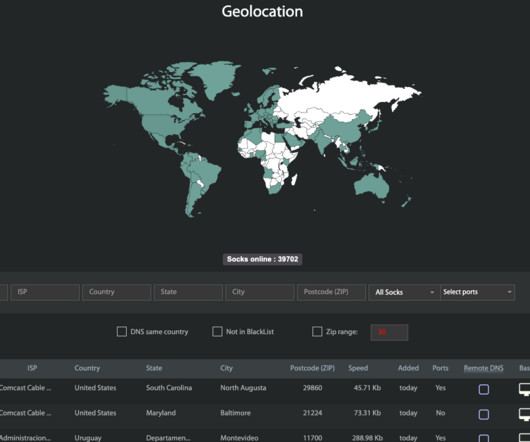
With the recent demise of several popular “proxy” services that let cybercriminals route their malicious traffic through hacked PCs, there is now something of a supply chain crisis gripping the underbelly of the Internet. com , a malware-based proxy network that has been in existence since at least 2010.









Let's personalize your content