Hyperautomation and the Future of Cybersecurity
eSecurity Planet
JUNE 22, 2022
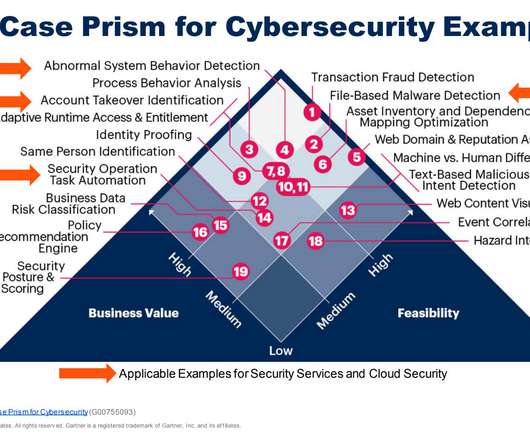
A blend of robotic process automation, machine learning technology, and artificial intelligence, hyperautomation seeks to refine and improve business and technology processes that previously required a human decision-maker. Hyperautomation incorporates artificial intelligence with automation tools, to increase scope and complexity.














Let's personalize your content