Soft-Launching and Open Sourcing the Have I Been Pwned Rebrand
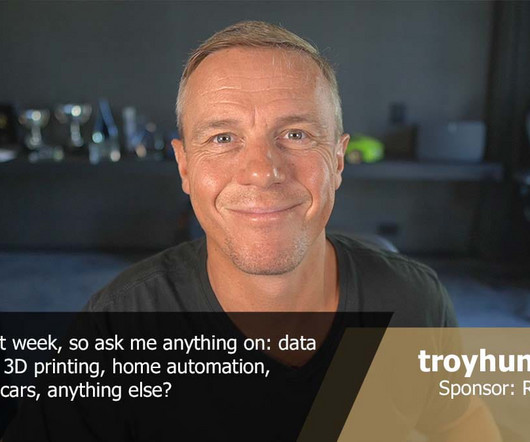
Troy Hunt
MARCH 11, 2025
Designing the first logo for Have I Been Pwned was easy: I took a SQL injection pattern, wrote "have i been pwned?" after it and then, just to give it a touch of class, put a rectangle with rounded corners around it: Job done! I mean really, what more did I need for a pet project with a stupid name that would likely only add to the litany of failed nerdy ideas I'd had before that?















Let's personalize your content