The Origins and History of the Dark Web
Identity IQ
FEBRUARY 8, 2024
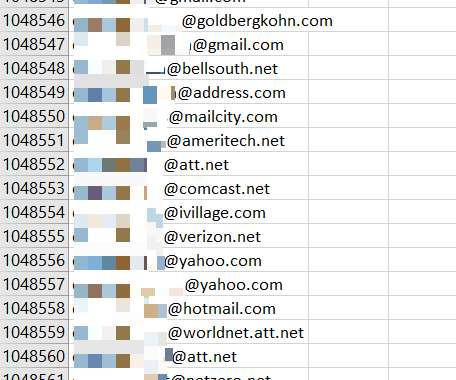
You probably use the deep web all the time — examples may include bank accounts, your email, and login-restricted content such as news or streaming entertainment. From 2011 to 2013, the Silk Road hosted 1.2 The FBI shut down the Silk Road in October 2013. The deep web is far and away the largest part of the internet.















Let's personalize your content