“FudCo” Spam Empire Tied to Pakistani Software Firm
Krebs on Security
SEPTEMBER 6, 2021
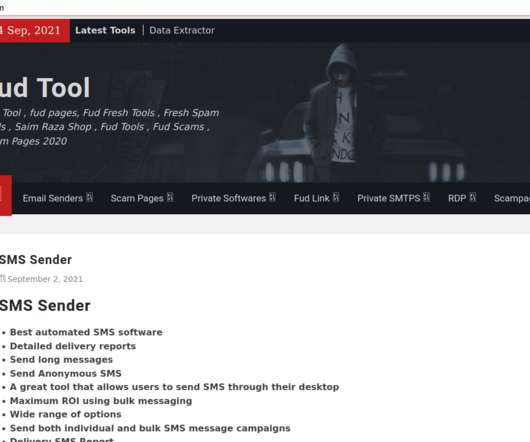
The common acronym in nearly all of Saim Raza’s domains over the years — “FUD” — stands for “ F ully U n- D etectable,” and it refers to cybercrime resources that will evade detection by security tools like antivirus software or anti-spam appliances. Also we are running business since 2006.”











Let's personalize your content