Why We Still Haven’t Learned From the Target Data Breach a Decade Later
Security Boulevard
MAY 17, 2023
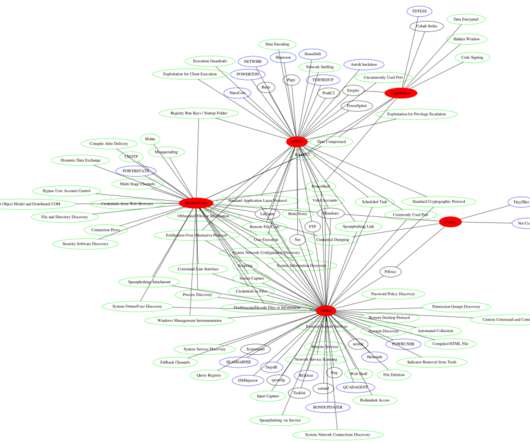
The threat actor’s methodology wasn’t unique — they used a six-step approach that can be mapped directly to cyber attack frameworks. Most of these steps could’ve been blocked with the aid of DNS protection. Though we still don’t know the identity of the attacker(s), we know they carried the attack in six basic steps.











Let's personalize your content