Anubis, a new info-stealing malware spreads in the wild
Security Affairs
AUGUST 27, 2020
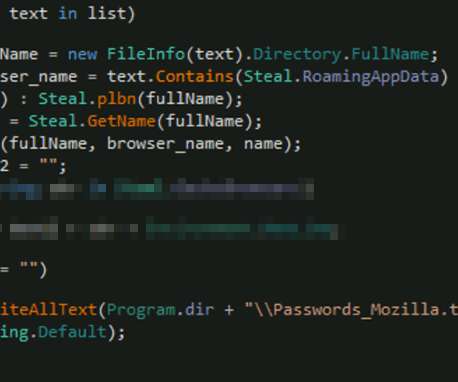
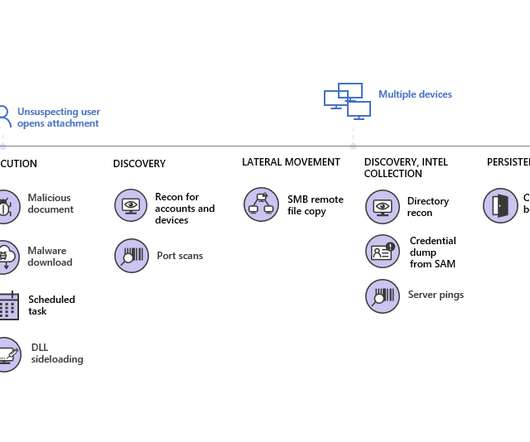
According to Microsoft, the new piece of malware uses code forked from Loki malware to steal system info, credentials, credit card details, cryptocurrency wallets. — Microsoft Security Intelligence (@MsftSecIntel) August 26, 2020. Copyright (C) 2014-2015 Media.net Advertising FZ-LLC All Rights Reserved -->.











Let's personalize your content