BEST PRACTICES: Mock phishing attacks prep employees to avoid being socially engineered
The Last Watchdog
MAY 1, 2019
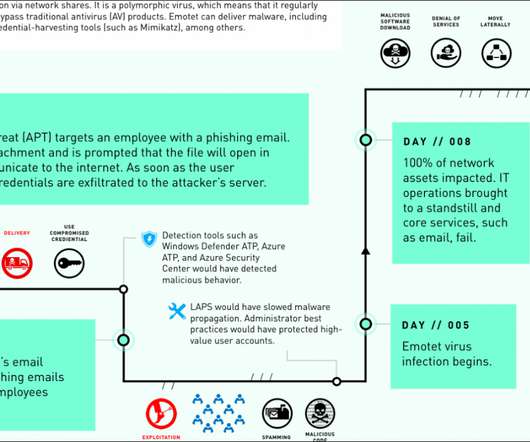
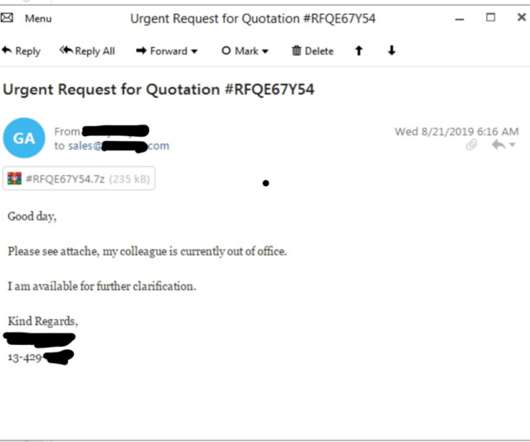
Despite billions of dollars spent on the latest, greatest antivirus suites, firewalls and intrusion detection systems, enterprises continue to suffer breaches that can be traced back to the actions of a single, unsuspecting employee. Social engineering, especially phishing, continues to trigger the vast majority of breach attempts.


















Let's personalize your content