Arrest, Raids Tied to ‘U-Admin’ Phishing Kit
Krebs on Security
FEBRUARY 8, 2021
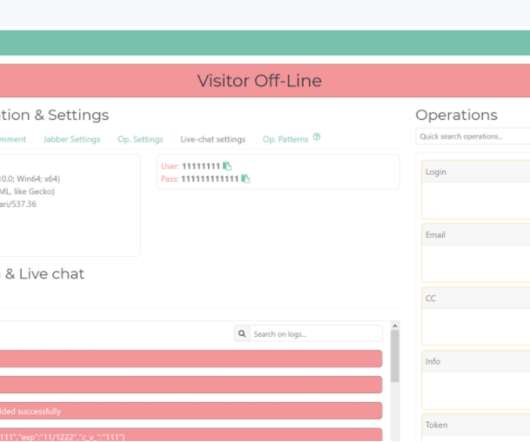
Brad Marden , superintendent of cybercrime operations for the Australian Federal Police (AFP), said their investigation into who was behind U-Admin began in late 2018, after Australian citizens began getting deluged with phishing attacks via mobile text messages that leveraged the software. The U-Admin phishing panel interface. Image: fr3d.hk/blog.









Let's personalize your content