FBI and CISA published a new advisory on AvosLocker ransomware
Security Affairs
OCTOBER 13, 2023
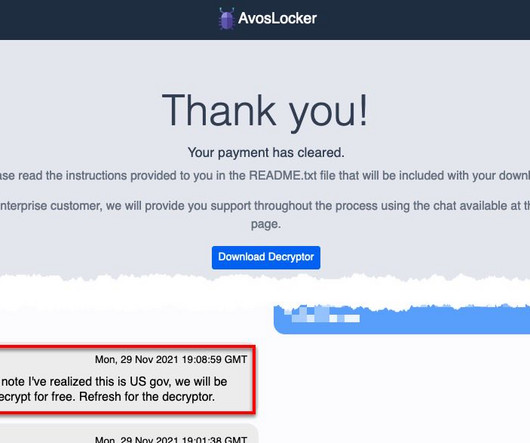
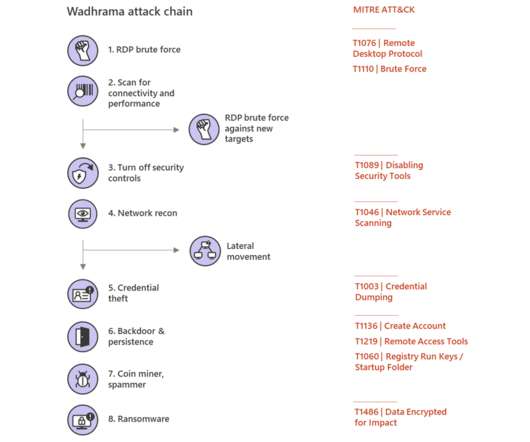
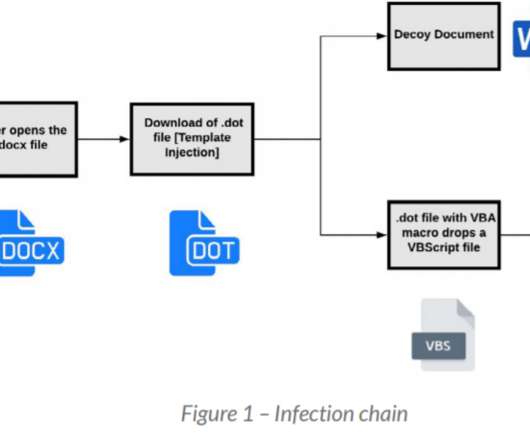
FBI and CISA published a joint Cybersecurity Advisory (CSA) to disseminate IOCs, TTPs, and detection methods associated with AvosLocker ransomware. The joint Cybersecurity Advisory (CSA) is part of an ongoing #StopRansomware effort aimed at sharing technical details associated with various ransomware operations.









Let's personalize your content