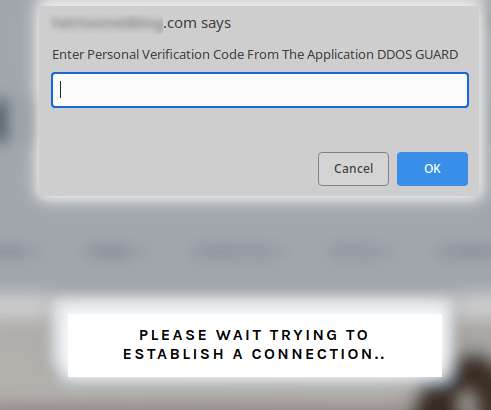
Fake DDoS protection pages on compromised WordPress sites lead to malware infections
Security Affairs
AUGUST 21, 2022
The scripts will also infect the victim’s computer with the Raccoon Stealer info-stealing trojan which allows operators to steal login credentials, cookies, auto-fill data, and credit cards saved on web browsers, along with cryptocurrency wallets. Follow me on Twitter: @securityaffairs and Facebook. Pierluigi Paganini.















Let's personalize your content