New Windows Meduza Stealer targets tens of crypto wallets and password managers
Security Affairs
JULY 3, 2023
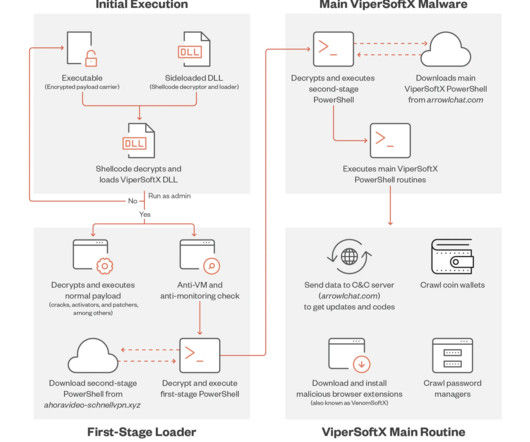
The malware also targets crypto wallet extensions, password managers, and 2FA extensions. “What’s more concerning is that a large portion of antivirus software has proven ineffective against the Meduza stealer binary, either failing to detect it statically or dynamically” reads the analysis published by Uptycs.














Let's personalize your content