One Year Later: What Have We Learned Since the Colonial Pipeline Attack
Thales Cloud Protection & Licensing
MAY 9, 2022
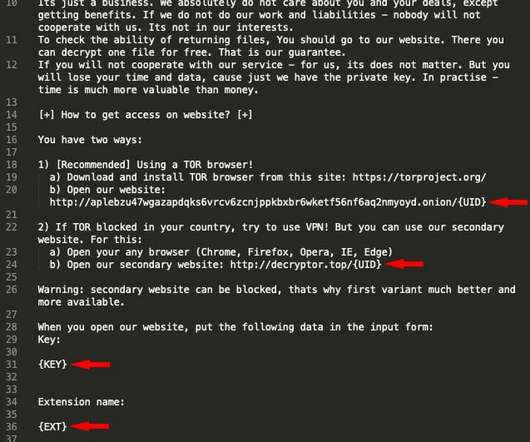
While implementation of security technologies such as multi-factor authentication and encryption have slightly increased, we have not yet reached the level where the majority of applications, data and operational technology are fully protected. Government Towards a Zero Trust Architecture dictate U.S.














Let's personalize your content