Cisco Secure Firewall on AWS: Build resilience at scale with stateful firewall clustering
Cisco Security
NOVEMBER 9, 2022
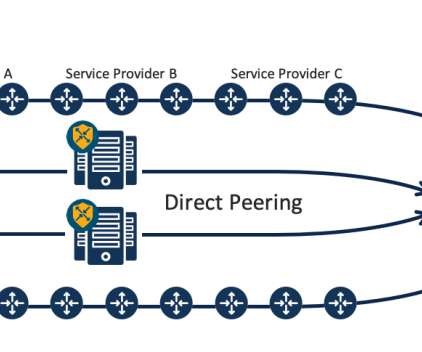
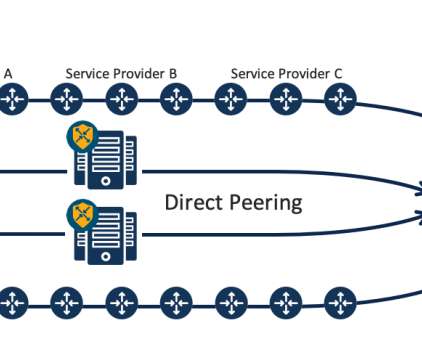
Organizations may introduce multiple individual firewalls into their AWS infrastructure to produce this outcome. To solve these challenges, Cisco created stateful firewall clustering with Secure Firewall in AWS. Cisco Secure Firewall clustering overview. In the Secure Firewall Threat Defense 7.1

















































Let's personalize your content