The Ongoing Cyber Threat to Critical Infrastructure
Thales Cloud Protection & Licensing
JULY 21, 2022
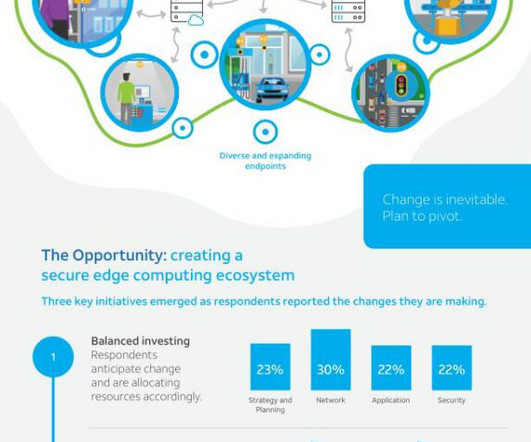
The Ongoing Cyber Threat to Critical Infrastructure. With that in mind, Thales has launched the 2022 Thales Data Threat Report Critical Infrastructure Edition, which includes responses from 300 security leaders and practitioners within critical infrastructure organizations. Thu, 07/21/2022 - 12:28.















Let's personalize your content