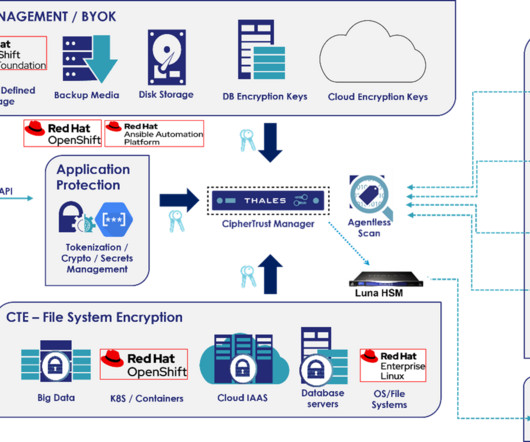
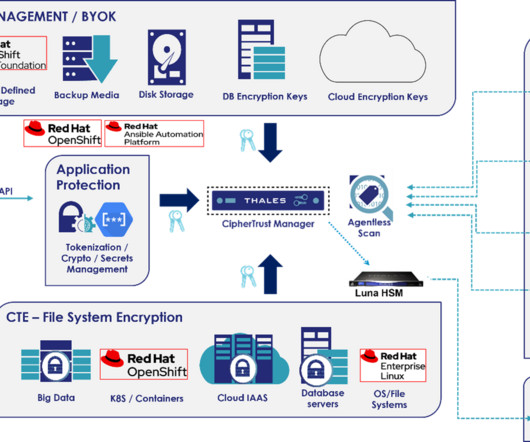
How Thales and Red Hat Protect Telcos from API Attacks
Thales Cloud Protection & Licensing
FEBRUARY 21, 2024
Legacy Technology Clashes : Most Telcos have very large legacy IT footprints. This unfortunately does not always integrate well with more modern technologies such as containerized or Kubernetes-based cloud-native applications. The more variations in the environment, the more complicated it is to manage.











Let's personalize your content