How to Write Spotless Job Description to Attract Cybersecurity Pros to Your Business
CyberSecurity Insiders
FEBRUARY 9, 2021
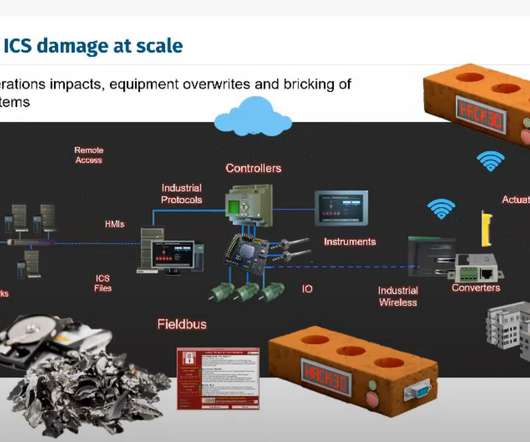
Whether you specialize in SaaS, outsource your services or operate as a physical goods trader in the B2B sector, the risk of cybersecurity intrusions prevails. According to CNBC , 43% of cybersecurity attacks are aimed at small businesses, however, only 14% are prepared to defend themselves.





















Let's personalize your content