What Damage Can Happen If Data Leaks When Quantum Computing Breaks Today’s Encryption
Joseph Steinberg
JANUARY 19, 2022
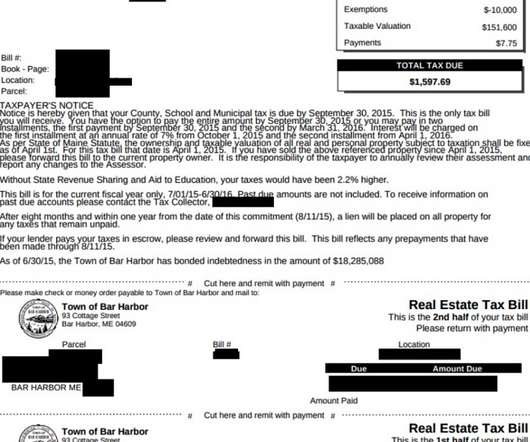
At some point in the not-so-distant future, quantum computers are going to pose a major threat to today’s encryption mechanisms and encrypted data. To begin with, all of today’s encrypted communications could potentially be at risk of being leaked and abused.










































Let's personalize your content