Artificial intelligence (AI) as an Enabler for Enhanced Data Security
Security Affairs
FEBRUARY 11, 2025
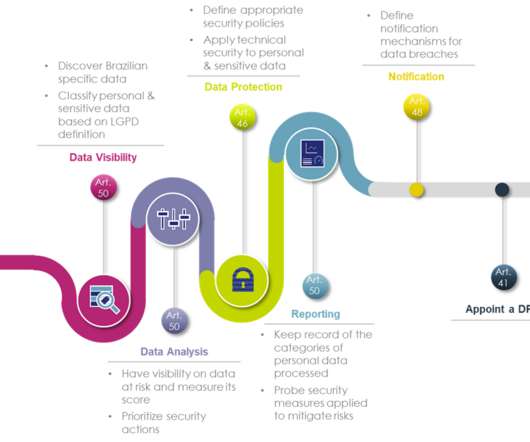
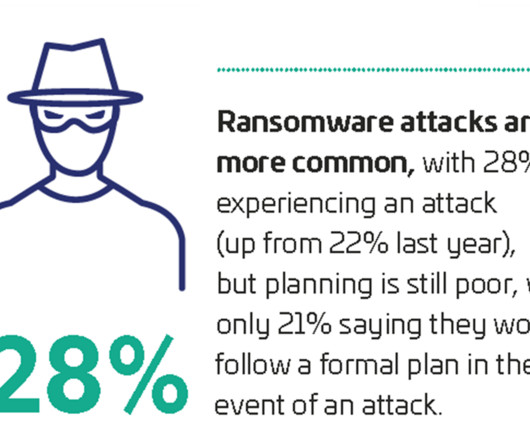
While AI introduces certain risks, its power to proactively identify and close data security gaps offers unparalleled protection when applied effectively. By leveraging AI across key data layers, organizations can discover, classify, and safeguard sensitive information to stay ahead of evolving threats.


















Let's personalize your content