How Thales and Red Hat Protect Telcos from API Attacks
Thales Cloud Protection & Licensing
FEBRUARY 21, 2024
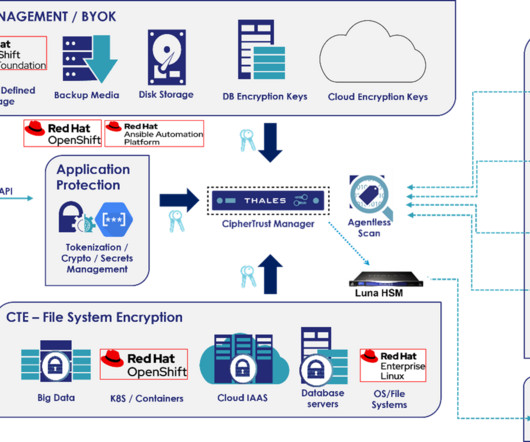
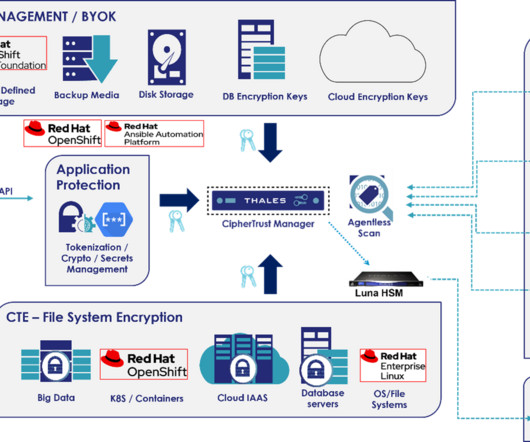
How Thales and Red Hat Protect Telcos from API Attacks madhav Thu, 02/22/2024 - 04:55 Application programming interfaces (APIs) power nearly every aspect of modern applications and have become the backbone of today’s economy. Encryption ensures the data itself cannot be accessed, even if intercepted during a “Man-in-the-Middle” attack.









Let's personalize your content