Fla. Man Charged in SIM-Swapping Spree is Key Suspect in Hacker Groups Oktapus, Scattered Spider
Krebs on Security
JANUARY 30, 2024
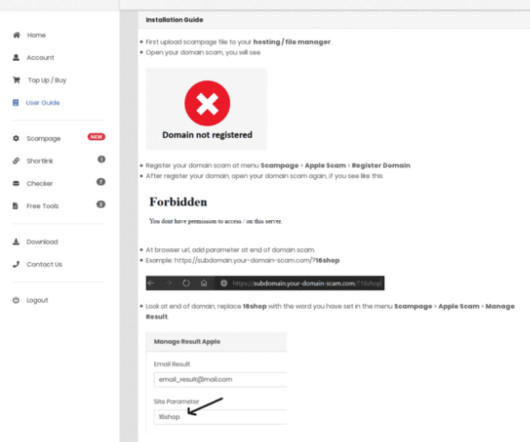
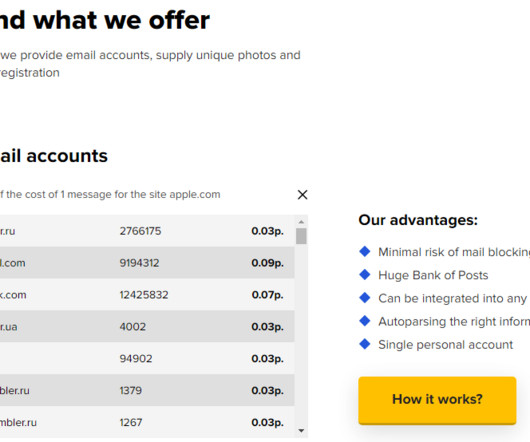
Those who submitted credentials were then prompted to provide the one-time password needed for multi-factor authentication. LastPass said criminal hackers had stolen encrypted copies of some password vaults, as well as other personal information. A booking photo of Noah Michael Urban released by the Volusia County Sheriff.













Let's personalize your content