A novel PayPal phishing campaign hijacks accounts
Security Affairs
JANUARY 11, 2025
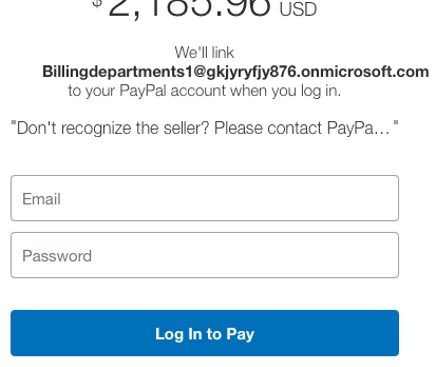
Fortinet warns of a phishing campaign using legitimate links to hijack PayPal accounts, tricking users into granting unauthorized access. Fortinet uncovered a phishing campaign targeting PayPal users. The scheme employs legitimate links to deceive victims and gain unauthorized access to their accounts. The phishing emails mimic PayPal notifications, including payment details, warnings, a real PayPal sender address, and a genuine URL to bypass security checks.















Let's personalize your content